Online trademark threats are on the rise, and they can have a devastating impact on businesses of all sizes. From counterfeiting to NFTs and social media impersonation, these threats can steal revenue from you, damage your reputation, erode your customer’s trust in your brand, and even put your consumers at risk of physical harm.
The Types of Threats to Your Trademarks
In this article, we'll discuss the most common online trademark threats that businesses need to be aware of to keep their brands safe, namely:
- Counterfeiting
- Knock-offs and Dupes
- Rogue Websites
- Trademark Squatting and Cybersquatting
- NFTs
- Social Media Impersonation
Let’s dive right in.
Counterfeiting
By now, we’re all familiar with counterfeiting. It’s the production and sale of goods that are made to imitate existing products. They infringe on trademarks and other IP that brands use to communicate the source and the quality of the products itself to their customers.
Counterfeits pose a major threat to brands in a number of ways, by:
- Taking away sales from the legitimate brand by fooling customers into thinking they are getting the real product, or by offering cheaper alternatives to popular products to consumers for whom the label is more important than the product itself.
- Eroding brands’ reputations by flooding the market with low-quality products that bear brands’ trademarked names and logos and causing confusion among consumers.
- Leaving legitimate brands to handle product returns and complaints from customers who are unaware that they got a fake product.
There has been a rapid increase in the amount of counterfeit products in the market in recent years, pushed by a number of factors, including the exploding popularity of online shopping, e-commerce functionalities added to social media, and greater access to key technologies.
Counterfeit goods can be particularly dangerous to consumers in industries like cosmetics, healthcare, food, and many more. Consumer danger comes in if these products don’t meet safety standards or if they’re made with inferior or hazardous materials.
Knock-offs and Dupes
Knock-off products, also known as dupes, are similar to counterfeits, but have some key differences that make them considerably harder to prevent.
The main distinction between counterfeits and knock-offs being that, while counterfeits are intentionally created to imitate the original product as closely as possible in order to deceive consumers, knock-offs are made as a cheap alternative to the original without overtly infringing on IP.
These dupes will copy the overall design of the original product, but will avoid elements that can be clearly proven to copy the original. They will avoid using brand names, logos, and distinctive elements of trade dress. Their listings in online marketplaces will also generally avoid using trademarked elements or brands’ copyrighted images.
This results in a product that’s exceedingly difficult to remove from online marketplaces without a thorough understanding of IP protection. It often means that a close relationship with the teams behind online marketplaces and social media networks will be necessary in order to properly enforce brands’ IP.
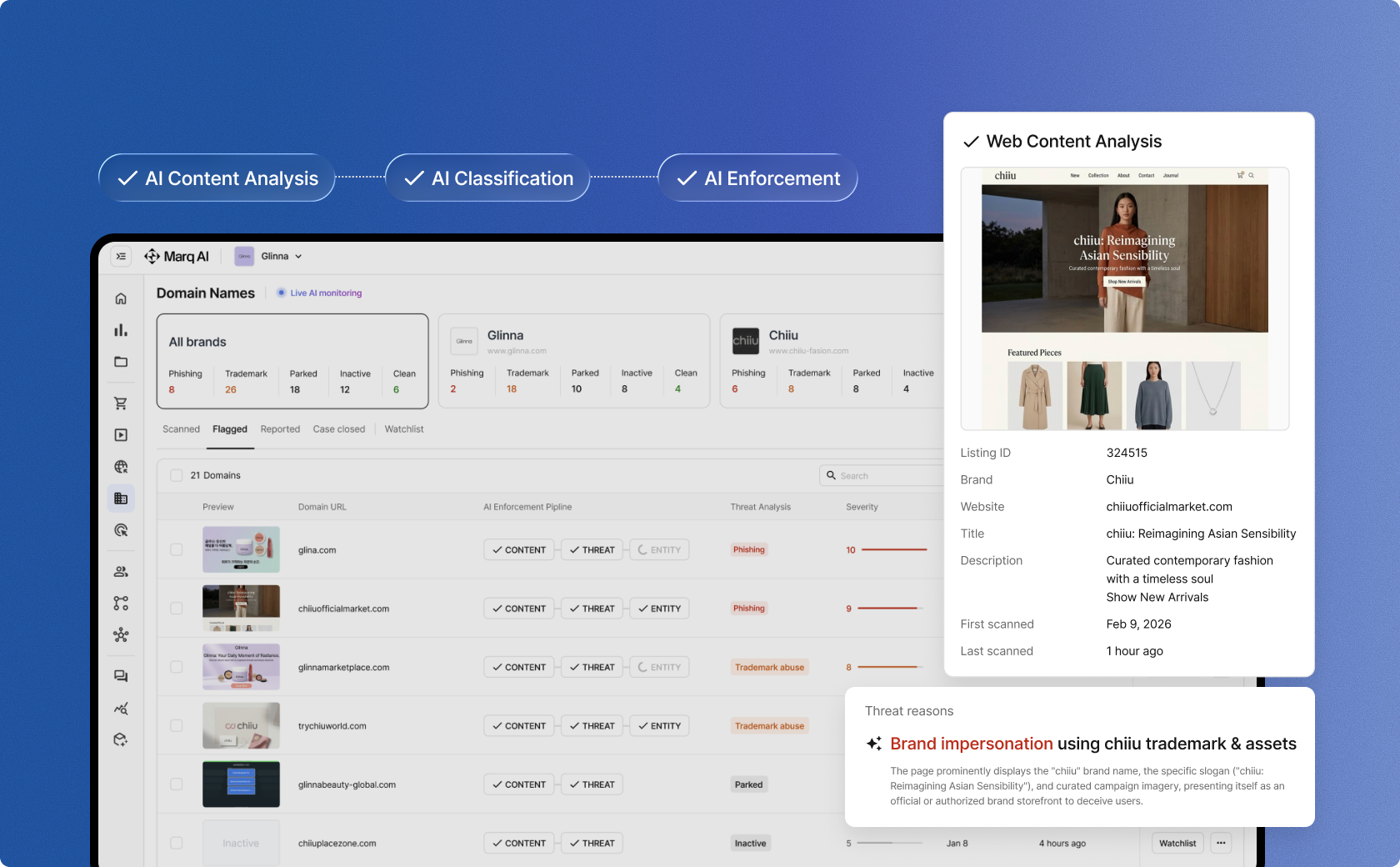
Rogue Websites
Rogue websites are malicious sites created to fool consumers into thinking they are visiting a known brand’s actual website. By using a brand’s trademarked names and logos, as well as their copyrighted images, they trick consumers into a false sense of security in order to commit online criminality.
These sites predominantly sell counterfeit products and use these sites as an additional layer of false legitimacy to confuse unwitting consumers. As many consumers still associate counterfeit products with sketchy street sellers, having a well-designed rogue website can portray enough authenticity to fool numbers of consumers into buying their products.
Though, rogue websites do have other uses for bad actors. They can be used in phishing and other scams, using the trusted company’s branding to steal consumers’ banking information and other personal details.
Trademark Squatting
Online trademark squatting, also known as cybersquatting, is a type of rogue website that involves registering a domain name containing a trademark owned by another party.
Along with the objectives mentioned above, squatters often register these domain names with the intention of selling them to the trademark owner at a profit.
These websites can also be used for redirects to online sales channels. By posting a link that could be confused for a legitimate brand’s website, and then immediately redirecting traffic to another website selling fake products, they can capture an audience of possible buyers who are unaware they’re on a rogue website.
NFT Trademark Infringements
The rise of non-fungible tokens (NFTs) has led to a new set of trademark infringement threats in recent years. NFTs can be used to represent a wide variety of digital assets, including artwork, music, videos, and even tweets.
However, as counterfeiters can create an NFT that features the trademark owner's logo or brand name, or that uses the trademark owner's copyrighted artwork, it poses a serious risk to the brand’s image online.
Trademark owners need to be aware of the potential for their trademarks to be used on NFTs without their permission.
In the past year, companies like Nike and Hermes were already taking legal action to protect their brands against counterfeit NFTs. Though NFTs aren’t now in the explosive bubble of 2022, they continue to exist, and are likely to experience a regrowth once the technology is refined and finds its proper niche.
Social Media Impersonation
Social media impersonation is the act of creating a fake social media account that is designed to look like the account of a legitimate brand.
Like rogue websites, fake social media accounts can often be used to sell counterfeit products, using the brand’s official logos and images to trick consumers into buying fake products. Imposters often use these accounts to solicit money, or damage the reputation of the real person or brand.
These impersonating accounts are increasingly used by trolls online to spread false information or to share harmful or extremist content.
By pretending to be the genuine brand while doing this, they can cause a significant audience of people to believe the posts come from the actual brand, sullying their reputation in the long term.
Key Takeaways For Brands
Trademark violations are growing fast in online spaces - not only in total industry size, but also in complexity and variety.
Threats like NFTs and sales through social media have arisen quickly in recent years, evolving the landscape of threats far beyond the simple sale of counterfeit products on sketchy websites.
For businesses to protect their IP today, it’s essential to have a full brand protection strategy. This involves keeping up with the ever-accelerating trends of technology that complexifies threats to IP, as well as the best practices for combating them.
As artificial intelligence has come to the forefront of modern culture and become accessible to everyone, these threats will only become more savvy, requiring an IP protection strategy that continues to outpace counterfeiters.
Stay up to date on the latest IP Protection content from MarqVision.
4 Enforcements a Week to 400: Scale Brand Safety with Marq AI

Don’t Just Find Counterfeits. Dismantle the Entire Network.

.png)
Discover the latest trends and challenges in IP protection

Take Control of Your Trademarks with MARQ Folio

Renew and Manage Your Trademarks Easily With MARQ Folio

We’re waiting to hear from you

See the best brand protection solution in action

Don’t let piracy steal your growth

Talk to us about your brand protection problems