Best Tools for Detecting Targeted Brand Phishing Attacks
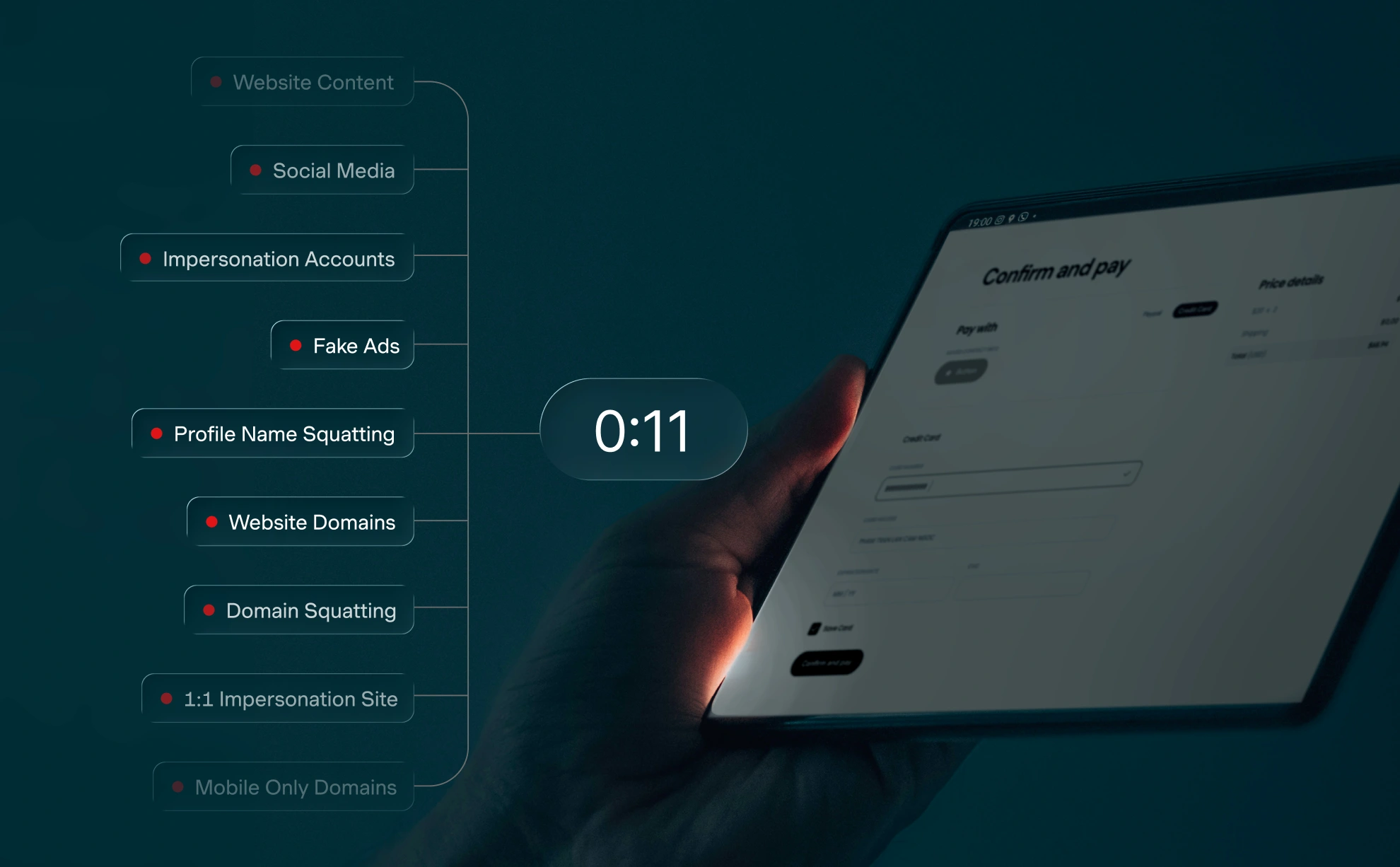
In 2026, targeted brand phishing has evolved into a high-speed, automated threat that bypasses traditional email filters. Effective defense now requires External Attack Surface Monitoring (EASM) to dismantle phishing infrastructure before they can harvest your customers' credentials.

Trusted by Global Brands & Financial Institutions






















Why are traditional security tools failing against modern spear phishing?
Traditional internal security controls are insufficient because the attack surface has shifted beyond the corporate inbox. Attackers now use AI to deploy polymorphic campaigns, creating clones of brand storefronts in minutes that are pixel-perfect and hard to detect. Real-time lookalike domain detection and takedowns are essential to close this window.
This creates a critical 'window of vulnerability' where a look-alike domain can be registered and start harvesting data in under 60 minutes (CybelAngel, 2026). When unauthorized sellers hijack your brand identity, they don't just steal data; they drain Buy Box share, erode margins, and create massive channel conflict.
How does MarqVision turn phishing chaos into clear operational action?
MarqVision treats brand abuse as an external security vulnerability managed through data and automation. Unlike legacy tools focused solely on manual takedowns, our platform provides diagnostic clarity to identify the patterns behind the attacks.
Atomic Product Detections™
Identify infringing sites and products even when logos are blurred or hidden to evade standard scanners. Detect 99%+ of brand abuse with Generative AI.
Exposure Delta Analysis
We don't just show a list of links; we show you the exposure delta, allowing you to prioritize the high-risk operators driving the most commercial harm.
Revenue Recovery Strategy
Shift brand protection from a legal expense to a revenue-generating strategy that mitigates counterfeit impact on revenue, safety, and brand equity.
What features are essential for a 2026 phishing detection tool?
To maintain pricing integrity and brand control in an AI-driven environment, your security stack must include these four core capabilities to reduce financial losses by an estimated 30-40% (CybelAngel, 2026).
See Platform in ActionReal-time Registration Alerts
Flag look-alike domains and typosquatting the moment they are registered.
Cross-Platform Coverage
Monitor beyond the web—including TikTok, Instagram, and even Web3/NFT platforms.
High-Velocity Automation
The takedown benchmark is now <5 minutes. Marketplace enforcement software with 24/7 scanning is required to achieve this.
SIEM/SOAR Integration
Direct API flows into Security Information and Event Management (SIEM) or Security Orchestration, Automation, and Response (SOAR) tools like Splunk or Azure Sentinel via HTTPS to reduce Mean Time to Respond.
MarqVision vs Legacy Brand Protection: What is the difference?
Modern platforms like MarqVision have reduced the transition to active enforcement to just 2–3 weeks, compared to the 6+ months required by traditional providers. See how we stack up in our MarqVision vs ZeroFox comparison.
| Feature | Legacy Solutions | MarqVision |
|---|---|---|
| Detection Method | Keyword & Basic Image Match | Generative AI & Semantic Analysis |
| Takedown Speed | 24 - 48 Hours | Under 5 Minutes |
| Focus | Manual Takedowns | Revenue Recovery & Saturation Rate |
| Analysis | Individual Listings | Actor Clustering & Seller Intelligence |
| Onboarding | 6+ Months | 2 - 3 Weeks |
Frequently Asked Questions
How do AI clones impact spear phishing?
Attackers use generative AI to create high-fidelity replicas of brand websites and even executive voices. These clones allow for automated, high-conversion credential harvesting. Effective defense requires visual recognition tools that spot brand misuse even when logos are modified or blurred (MarqVision, 2026).
How does brand impersonation differ from standard phishing?
Standard phishing relies on generic deceptive messages to steal credentials, whereas targeted brand impersonation involves creating highly realistic replicas of your digital presence. Attackers clone websites, social media profiles, and domains to hijack your brand's established trust and deceive your specific customer base.
Why is manual detection ineffective against fake storefronts?
Threat actors now use automation and AI to register typosquatted domains and deploy fake storefronts in under an hour. Manual detection cannot scale or react fast enough to catch these polymorphic campaigns. Continuous monitoring and automated enforcement are critical to dismantling these impersonation sites before they cause damage.
Stop brand impersonation and protect your customers
Don't let targeted phishing campaigns and fake storefronts hijack your brand's trust. Automatically detect and take down impersonation infrastructure before it causes damage.